22.16.Solution for Outlook security patches through GPO
Important information
The security updates for Outlook released on September 12, 2017 are affecting the contentACCESS email archive. The users are no longer able to open the original archived messages from shortcuts, only the shortcut itself. This is caused by the Microsoft’s decision to disable Outlook form scripting by default.
After installing the security updates for Outlook, emails that were archived by third-party application are showing an unwanted behavior. All programs and applications using custom Outlook forms are affected. More information can be found here.
The Outlook form scripting is disabled by default, but it can be enabled using registry keys as described in the section mentioned above. This section describes the solution for the Outlook security patches through Group policy (GPO).
The GPO solution
This solution consists of three steps:
1) Preparing the Distribution point
2) Creating the group policy object and assign it to the affected machines
3) Checking the changes
Preparing the Distribution point
To use the GPO for the solution, a distribution point has to be created on the publishing server:
- Log on to the server computer (Domain controller) as an administrator.
- Create a shared network folder that will contain the CustomFormFix folder that you want to distribute. Extract the CustomFormFix.zip to this folder.
Note: Registry key for MS Outlook 2016 works also with MS Outlook 2019.
- Set permissions on the shared folder to allow access to the distribution point (everyone should have at least read access).
- In this demo case the distribution group path is \\SharedFolder.
Creating the group policy object and assigning it to the affected machines
To apply the solution, a new group policy object should be created and the CustomFormsFix.ps1 PowerShell script should be set in the GPO:
- Start the group policy management on the domain controller.
- Create a new group policy object in your domain.
- Link the newly created GPO object to your domain.
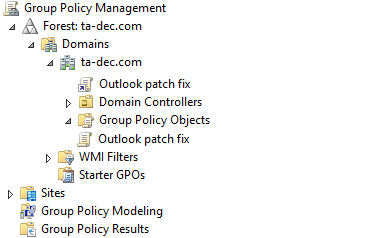
- Set the Security filtering for the required computers (in our case we chose the Domain computers group).
- Right click and choose Edit on the new GPO.
- Choose the Compute configuration -> Windows Settings -> Scripts -> Startup option.
- In the Startup properties windows choose the PowerShell Scripts tab.
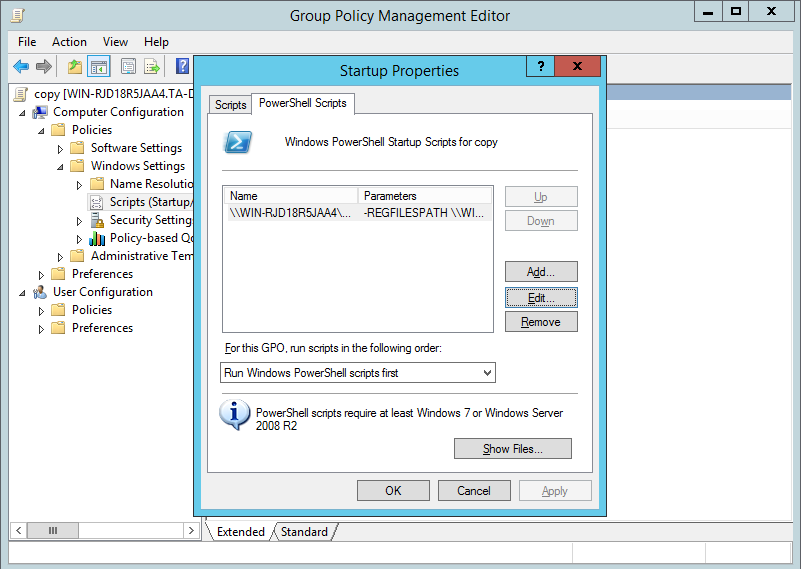
- Click on the Add button and create a new configuration.
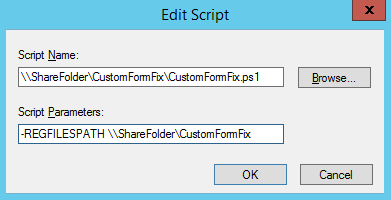
The script name in our case is: \\ShareFolder\CustomFormFix\CustomFormFix.ps1 (the shared path of the extracted PowerShell script) and the Script Parameters is -REGFILESPATH \\ShareFolder\CustomFormFix (the –REGFILESPATH parameter plus the shared path of the earlier created CustomFormFix folder).
Checking the changes
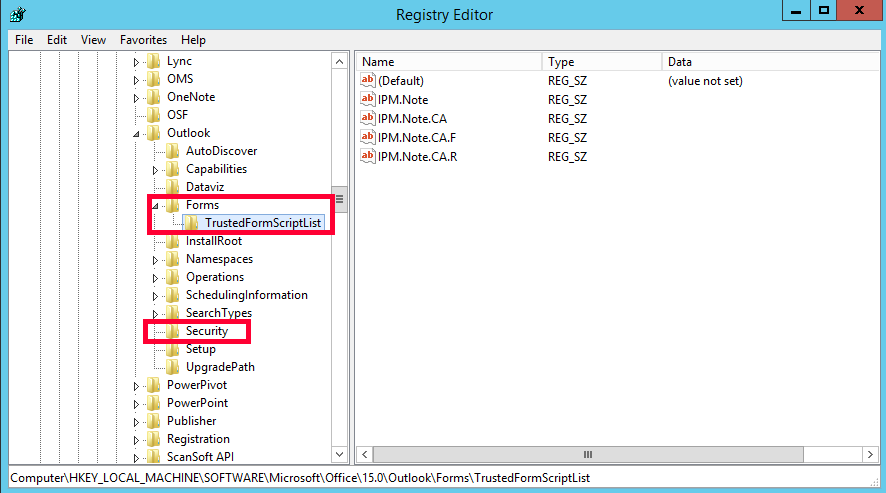
To check if our configuration and GPO deployment was successful, it’s necessary to restart the client machine, which was set in the Security filtering:
- Open the Registry Editor (regedit.exe)
- Find the path
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ or the path HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\
and open the Outlook KEY, which is created by your office version, for example:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\15.0\Outlook - There should be two new keys in this folder: Forms and Security